Commentary: Big Tent Ideas
MIKE CONAWAY: As China Espionage Threat Widens, America Must Lock Down Its Own House
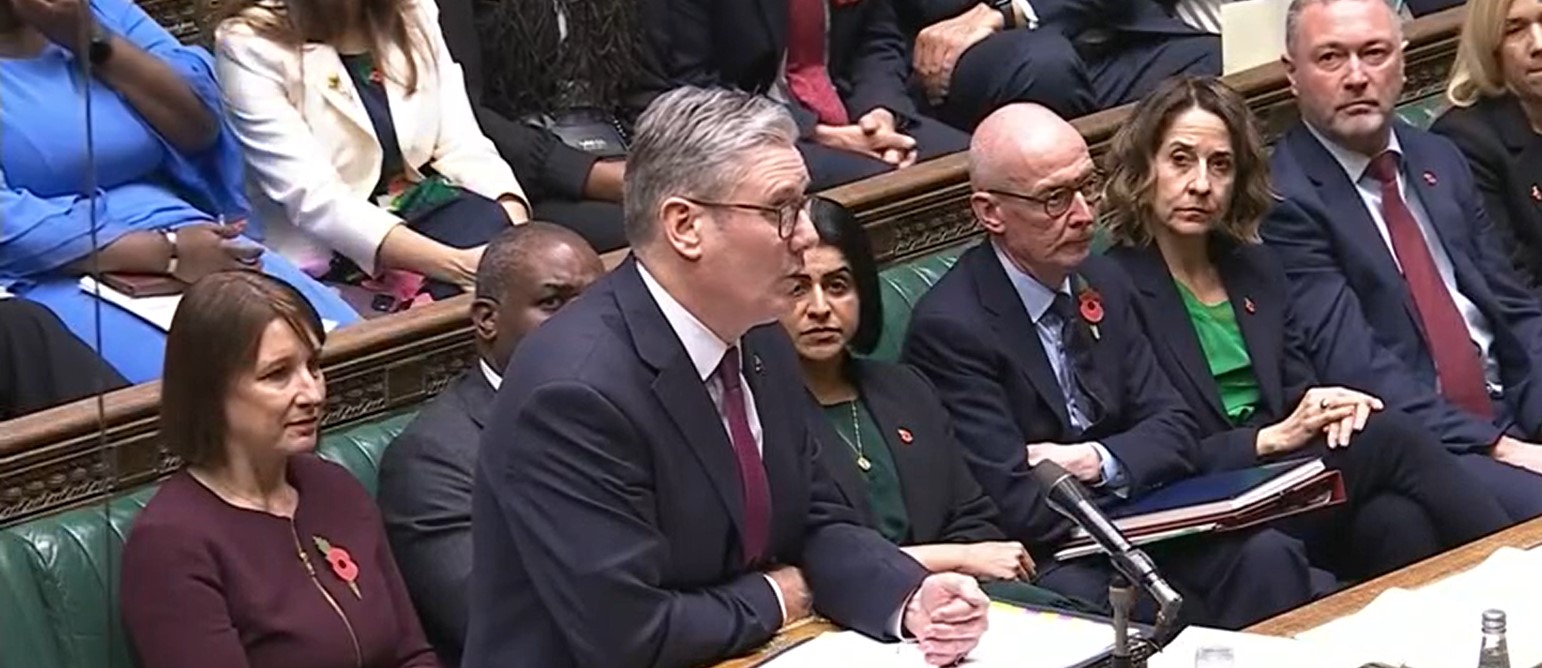
(Screen Capture/CSPAN)
British Prime Minister Keir Starmer stands a respectable 5’8”, but during his recent visit to China he was — as the kids say — “mogged.”
Soldiers of the People’s Republic’s honor guard, all more than six feet tall, towered over him on both sides.
The optics were hard to miss. The empire that once humiliated China into opening its ports and surrendering Hong Kong now approached Beijing like Oliver Twist asking for more gruel.
Back in London, the symbolism turned operational.
Just days before Starmer’s trip, the British government approved construction of a massive new Chinese “mega-embassy.” Heavily redacted plans reportedly include a sprawling underground complex — hundreds of rooms, one positioned alarmingly close to a fiber-optic cable carrying some of Britain’s most sensitive data.
Everyone understands this is reckless. It’s happening anyway.
The standard explanation is economics. Britain’s growing dependence on cheap Chinese imports has made confrontation uncomfortable. Beijing’s model — currency manipulation, wage suppression, and heavy state subsidies— has systematically hollowed out the industrial bases of its trading partners, buying silence along the way.
One British lawmaker put it bluntly: approving the embassy amounted to “surrendering our security for Chinese trade.”
But the deeper problem isn’t just Britain or even China’s overseas footprint. It’s that the Chinese Communist Party is relentlessly stealing Western military and technological secrets, and we have made it far too easy for them to do so.
For decades, China’s rise has depended less on innovation than on appropriation. Designing weapons systems, building advanced manufacturing processes, and developing proprietary technologies takes time and money. Stealing them is faster.
The weak link isn’t some exotic cyber exploit. It’s American citizens.
Unsecured cell phones, smartwatches, tablets, and wireless accessories routinely make their way into government buildings, military installations, and intelligence facilities that explicitly prohibit them. The rules exist. Enforcement does not.
Most violations aren’t malicious. People assume their intent matters more than their behavior. They forget that modern devices are persistent sensors — microphones, cameras, transmitters — and that compromise doesn’t require cooperation. A cellphone user doesn’t need a traitor. For China to get what it wants, the device just needs to be present in a place with sensitive information.
This creates perfect cover for the few who do have hostile intent.
According to former intelligence officials, and as noted in a recent analysis from former Trump National Security Council Chief of Staff and current America First Policy Institute Vice President Fred Fleitz, fewer than a small fraction of sensitive U.S. facilities have any reliable way to detect unauthorized wireless devices at all.
China benefits.
As the United States pours resources into next-generation systems — hypersonic weapons, nuclear modernization, missile defense, advanced submarines — Beijing is watching, copying, and racing to production. Not because they’re smarter, but because they’re stealing the blueprints.
Now add allies into the mix.
As countries like the U.K., Canada, and others deepen trade ties with China, intelligence environments become more porous. Shared facilities, joint programs, and coalition operations multiply the number of places where American secrets can leak, intentionally or otherwise.
Modern espionage thrives in exactly these gray zones: trusted partners, mixed-use spaces, unsecured wireless environments.
This is why America needs to hunker down and start coming to terms with what’s worked — and what hasn’t.
First, it should examine Intelligence Community Directive 705, the directive that set the intelligence community’s security standards for building Sensitive Compartmented Information Facilities (SCIFs) — the rooms/buildings where classified intel is handled.
ICD-705 was a sorely needed directive to protect America’s national security secrets. The problem is its cost. Its security requirements are so expensive that they have still yet to be implemented across much of the government nearly a decade later.
Renovating the current SCIFs to comply with ICD-705 can cost hundreds of dollars per square foot, adding up to tens of billions of dollars government-wide. As a result, thousands of SCIFs continue operating under temporary waivers to remain in operation even though they are not actually meeting all of the necessary security requirements.
Good news for China, bad news for us.
As the government continues exploring ways to get those costs down, one solution could be to deploy Wireless Intrusion Detection Systems (WIDS). This technology is capable of detecting unauthorized devices in secure spaces and can close the most dangerous gaps quickly and at a fraction of the cost.
Rather than tearing down walls and rebuilding facilities, WIDS can alert security teams the moment a prohibited device appears before the next generation of secrets walks out the door over the air.
At the same time, the U.S. must reconsider intelligence sharing and technology transfers with countries unwilling to take Chinese espionage seriously on their own soil. And yes, that includes tightening visa policies and limiting access to sensitive fields for nationals of adversary states. The scale of the threat demands it.
Critics will argue this is paranoid or heavy-handed. They said the same thing before China stole its way to near-peer military status.
The neoliberal fantasy that trade would tame authoritarian regimes is over. The only question left is whether America adapts to the reality of constant espionage — or keeps building China’s next generation of weapons for them.
Going it alone won’t be easy. But failing to secure our own house is no longer an option.
Mike Conaway is a former member of Congress who served on the Committee on Armed Services, including its Subcommittee on Intelligence, Emerging Threats the Permanent Select Committee on Intelligence
The views and opinions expressed in this commentary are those of the author and do not reflect the official position of the Daily Caller News Foundation.
(Featured Image Media Credit: Screen Capture/CSPAN)
All content created by the Daily Caller News Foundation, an independent and nonpartisan newswire service, is available without charge to any legitimate news publisher that can provide a large audience. All republished articles must include our logo, our reporter’s byline and their DCNF affiliation. For any questions about our guidelines or partnering with us, please contact [email protected].

